Hello Asterisk Team,
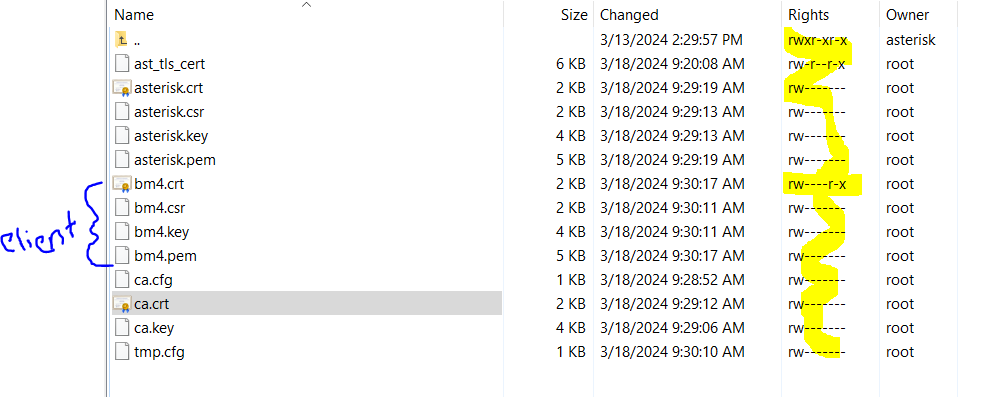
Working on PJSIP project, where SIP need to configure with Asterisk, after generating keys and certificate for Asterisk and client getting one error
Bellow error:
13:15:45.214 os_core_win32. !pjlib 2.14 for win32 initialized
13:15:45.226 sip_endpoint.c .Creating endpoint instance…
13:15:45.228 pjlib .select() I/O Queue created (000001BB5A4FA058)
13:15:45.231 sip_endpoint.c .Module “mod-msg-print” registered
13:15:45.231 sip_transport. .Transport manager created.
13:15:45.232 pjsua_core.c .PJSUA state changed: NULL → CREATED
13:15:45.245 sip_endpoint.c .Module “mod-pjsua-log” registered
13:15:45.245 sip_endpoint.c .Module “mod-tsx-layer” registered
13:15:45.247 sip_endpoint.c .Module “mod-stateful-util” registered
13:15:45.249 sip_endpoint.c .Module “mod-ua” registered
13:15:45.250 sip_endpoint.c .Module “mod-100rel” registered
13:15:45.253 sip_endpoint.c .Module “mod-pjsua” registered
13:15:45.254 sip_endpoint.c .Module “mod-invite” registered
13:15:45.297 wmme_dev.c …WMME found 2 devices:
13:15:45.302 wmme_dev.c … dev_id 0: Wave mapper (in=0, out=2)
13:15:45.304 wmme_dev.c … dev_id 1: Remote Audio (in=0, out=2)
13:15:45.309 wmme_dev.c …WMME initialized
13:15:45.311 pjlib …select() I/O Queue created (000001BB58F4FFE8)
13:15:45.327 sip_endpoint.c .Module “mod-evsub” registered
13:15:45.328 sip_endpoint.c .Module “mod-presence” registered
13:15:45.334 sip_endpoint.c .Module “mod-mwi” registered
13:15:45.335 sip_endpoint.c .Module “mod-refer” registered
13:15:45.340 sip_endpoint.c .Module “mod-pjsua-pres” registered
13:15:45.341 sip_endpoint.c .Module “mod-pjsua-im” registered
13:15:45.343 sip_endpoint.c .Module “mod-pjsua-options” registered
13:15:45.344 pjsua_core.c .1 SIP worker threads created
13:15:45.345 pjsua_core.c .pjsua version 2.14 for win32-6.2/x86_64/msvc-19.3.9 initialized
13:15:45.346 pjsua_core.c !.PJSUA state changed: CREATED → INIT
13:15:45.356 ssl_sock_ossl. OpenSSL version : 805306576
13:15:45.373 tlstp:5060 SIP TLS listener is ready for incoming connections at IP
13:15:45.378 pjsua_core.c PJSUA state changed: INIT → STARTING
13:15:45.386 sip_endpoint.c .Module “mod-unsolicited-mwi” registered
13:15:45.389 pjsua_core.c .PJSUA state changed: STARTING → RUNNING
13:15:45.427 pjsua_acc.c Adding account: id=sip:bm4@IP
13:15:45.430 pjsua_acc.c .Account sip:bm4@ip added with id 0
13:15:45.433 pjsua_acc.c .Acc 0: setting registration…
13:15:45.448 tlsc000001BB59 …TLS client transport created
13:15:45.460 tlsc000001BB59 …TLS transport ip is connecting to ip:5061…
13:15:45.460 pjsua_acc.c …Contact for acc 0 updated: sip:bm4@ip;transport=TLS;ob;reg-id=1;+sip.instance=“urn:uuid:00000000-0000-0000-0000-000032f68b0a”
13:15:45.468 pjsua_core.c …TX 625 bytes Request msg REGISTER/cseq=35387 (tdta000001BB593DABE8) to TLS IP:
REGISTER sip:IP;transport=tls SIP/2.0
Via: SIP/2.0/TLS IP;rport;branch=z9hG4bKPjbe1744ec89ba4b22996285c63cc16c58;alias
Max-Forwards: 70
From: sip:bm4@IP;tag=2ae71006a3784a868fce52a0b5733270
To: sip:bm4@IP
Call-ID: 4270fa857f5546718072dc356d91798a
CSeq: 35387 REGISTER
Supported: outbound, path
Contact: sip:bm4@IP;transport=TLS;ob;reg-id=1;+sip.instance=“urn:uuid:00000000-0000-0000-0000-000032f68b0a”
Expires: 300
Allow: PRACK, INVITE, ACK, BYE, CANCEL, UPDATE, INFO, SUBSCRIBE, NOTIFY, REFER, MESSAGE, OPTIONS
Content-Length: 0
–end msg–
13:15:45.469 ssl000001BB593 !CA certificates loaded from ‘C:path\ca.crt’
13:15:45.497 pjsua_acc.c …Acc 0: Registration sent
13:15:45.510 SSL !STATUS_FROM_SSL_ERR (status): Level: 0 err: <167772559> <error:0A00018F:SSL routines::ee key too small> len: 0 peer: IP
13:15:45.528 ssl000001BB593 Error loading certificate chain file ‘C:path\bm4.crt’: ee key too small
13:15:45.534 ssl000001BB593 Handshake failed on IP in connecting to IP: ee key too small
13:15:45.549 tlsc000001BB59 TLS connect() error: [code=494399] peer: IP: ee key too small
13:15:45.552 tsx000001BB593 Failed to send Request msg REGISTER/cseq=35387 (tdta000001BB593DABE8)! err=494399 (ee key too small)
13:15:45.553 pjsua_acc.c …SIP registration failed, status=503 (ee key too small)
13:15:45.560 pjsua_acc.c …Scheduling re-registration retry for acc 0 in 5 seconds…
*** On registration state: PJSIP_SC_TSX_TRANSPORT_ERROR ee key too small
13:15:45.567 pjsua_acc.c Disconnected notification for transport tlsc000001BB593CA3D8
13:15:45.567 sip_transport. .Transport tlsc000001BB593CA3D8 shutting down, force=0
13:15:45.568 sip_transport. Transport tlsc000001BB593CA3D8 is being destroyed due to timeout in idle timer
13:15:45.573 tlsc000001BB59 TLS transport destroyed with reason 494399: ee key too small
13:15:51.007 tlsc000001BB59 TLS client transport created
13:15:51.016 tlsc000001BB59 TLS transport IP is connecting to IP…